Broken Access Control: The basics

What is Access Control
As said in the last OWASP Top 10, between all the web vulnerabilities, broken access control is the most common one. Access control is a group of constraints applied to access certain resources or do certain actions.
Types of Access Control
There are three types of Access Control, but to explain them, pay attention to the image below:
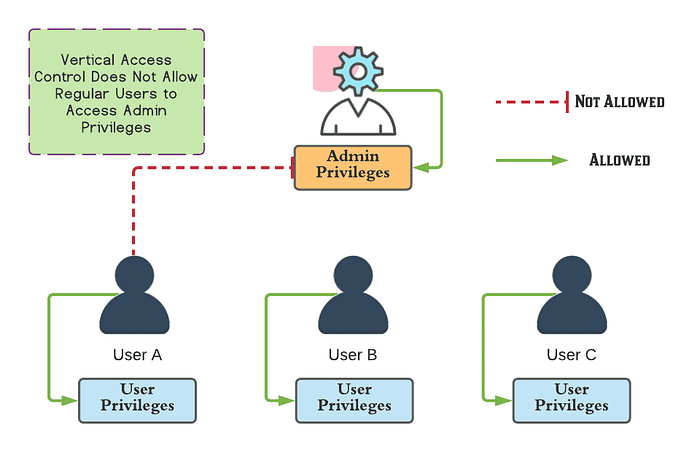
- Vertical Access Controls have restrictions that deny access to functions and resources not available to your type of user, for example in the image the User A cannot have access to admin privileges.
- Horizontal Access Control have restrictions that deny access to functions and resources not available to your user specifically, for example in the image the User A cannot have access to the User B password.
- Context-Dependent Access have restrictions bases on the state of the application that you are interacting, for example the User C cannot modify the items in theirs shopping cart if they already bought them.
Access control security models
An access control security model is a group of access control rules, that can be implemented in applications, networks, operating systems, and with other technologies. The most common models are as follows:
- Discretionary access control (DAC) has restrictions based on users and groups of users. In this model, the protected data has an owner, and the owner determine access permissions to users to the data.
- Mandatory access control (MAC) is a lot more restricted, it has restrictions that, unlike DAC, owners can’t modify access rights to the protected data.
- Role-based access control (RBAC) has named roles with access privilege assigned to them, and users are assigned to one or more roles. RBAC can provide manageable access control in complex applications, and is most effective when there are sufficient roles.
If you like it, read my other post about XSS here.
